Blocking a program in a firewall can vary in difficulty. Learn the steps of how to block programs in the most common firewalls.

A firewall protects computer systems from unwanted contact initiated by other computers connected over the internet or a network by blocking harmful programs based on user-defined rules. Individual services and applications can be granted access to pass through the firewall. This article explains how to block a program in a firewall to help you protect your system from unwanted access.
This tutorial on how to block a program in a firewall applies to computers running Microsoft Windows 11 operating system. Some details might vary slightly for Windows 10 or older versions, but the procedure is essentially the same.
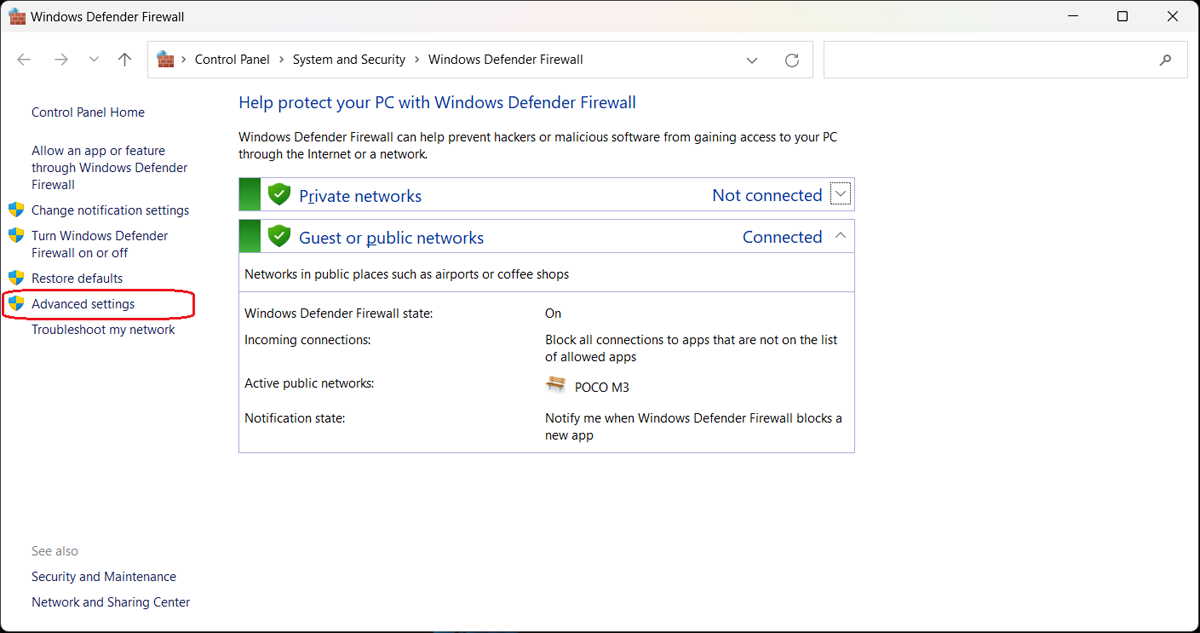
Use one of the following methods to open the Windows Defender Firewall with Advanced Security.
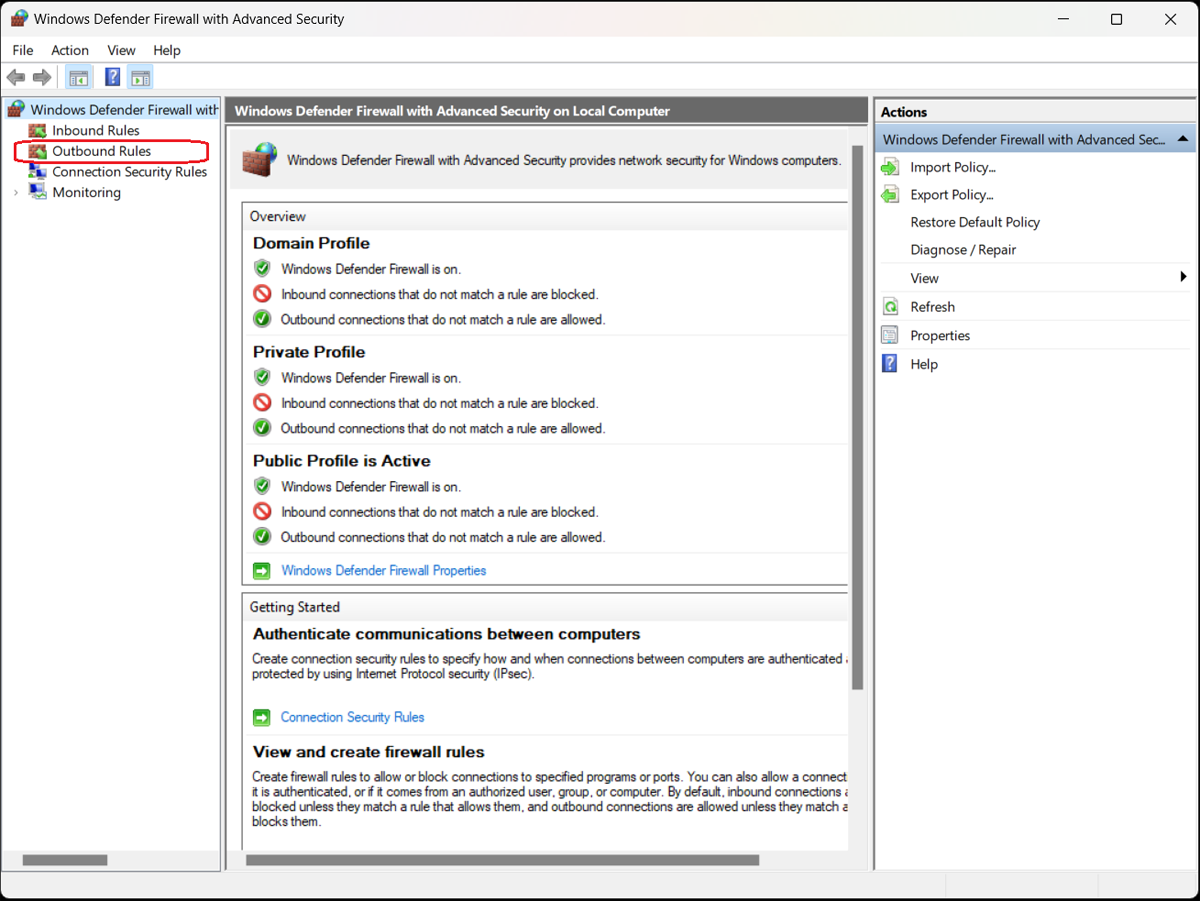
Choose whether you want to set an inbound rule allowing access to your computer for an external application or program, or an outbound rule allowing an application or program installed on your computer external access through the firewall.
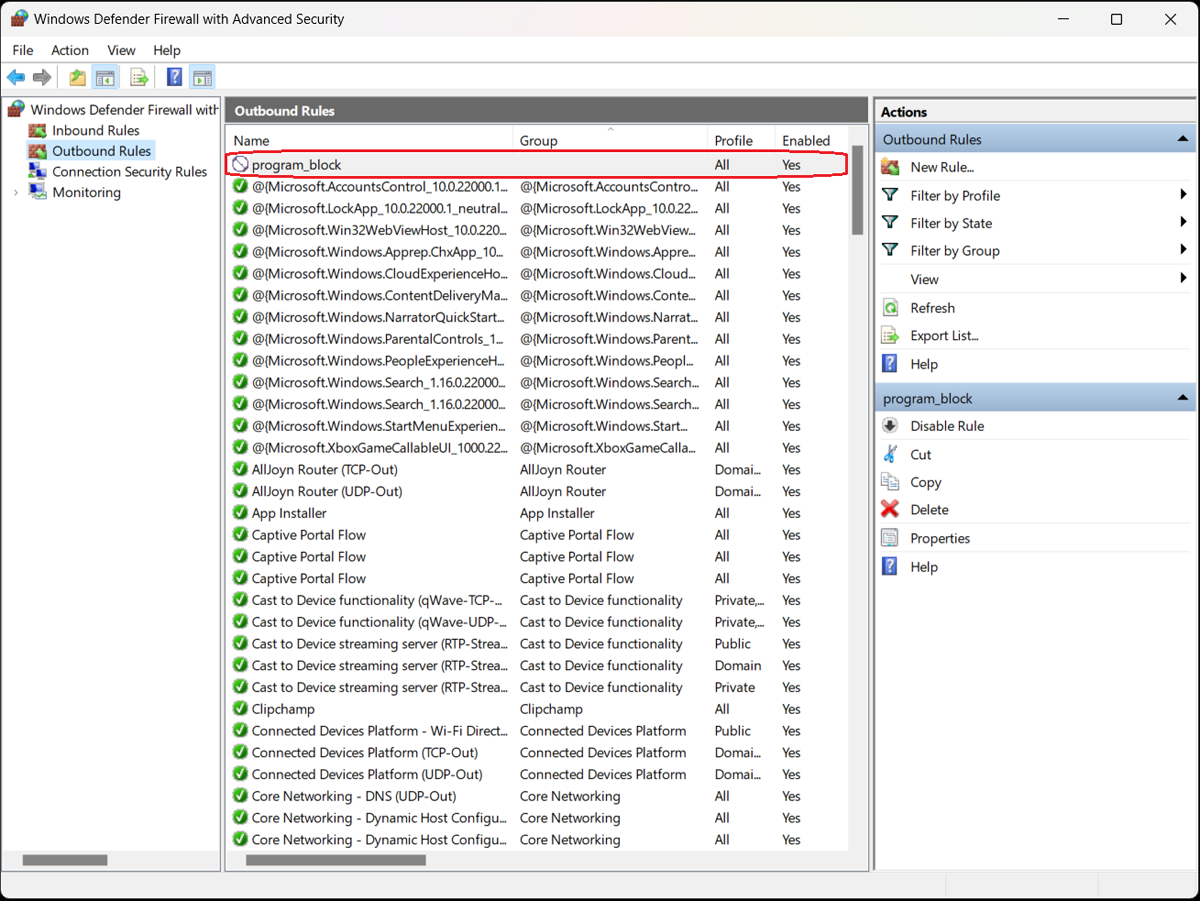
The program-blocking process is similar for both types of rules—for this example, we’ll choose Outbound Rules to block a program in the firewall.
Select the appropriate option from the left sidebar of the Windows Defender Firewall with Advanced Security screen. A list of outbound rules appears detailing their names, groups, profiles, and status (enabled/disabled).
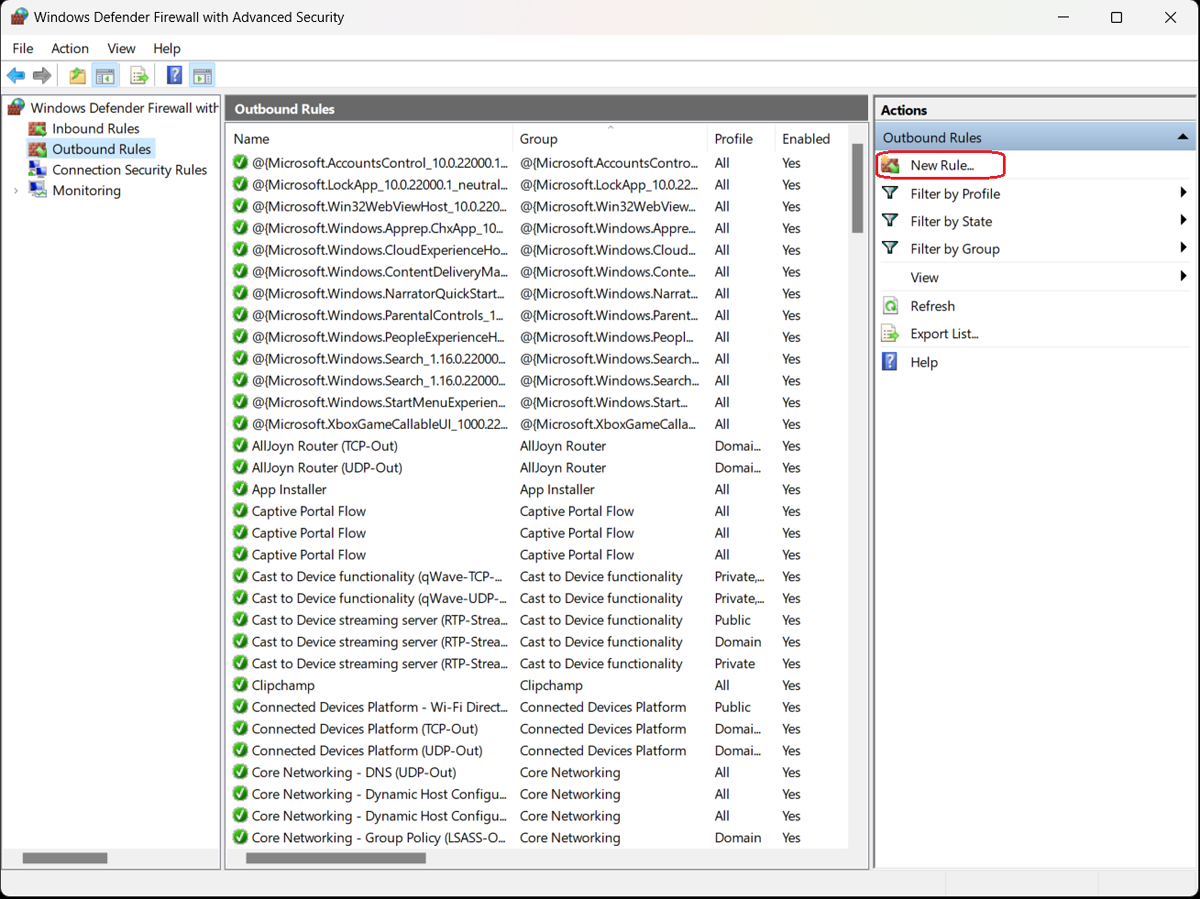
In the sidebar to the right of the list of existing outbound rules, click the “New Rule…” option. The New Outbound Rule Wizard opens, presenting four options for type of outbound rule:
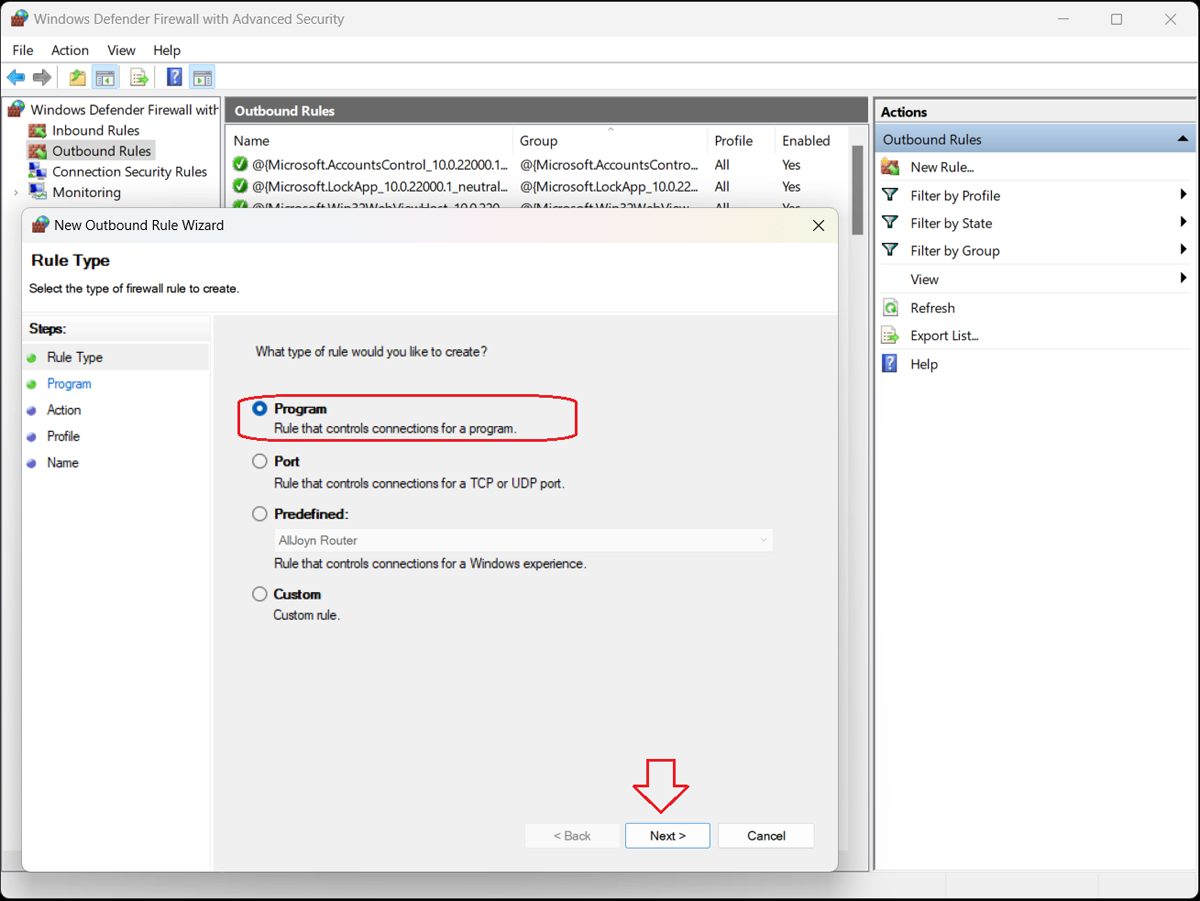
Select Program and click the “Next>” button. The Program dialog box opens to ask whether you want this rule to apply to all programs or just one specific program.
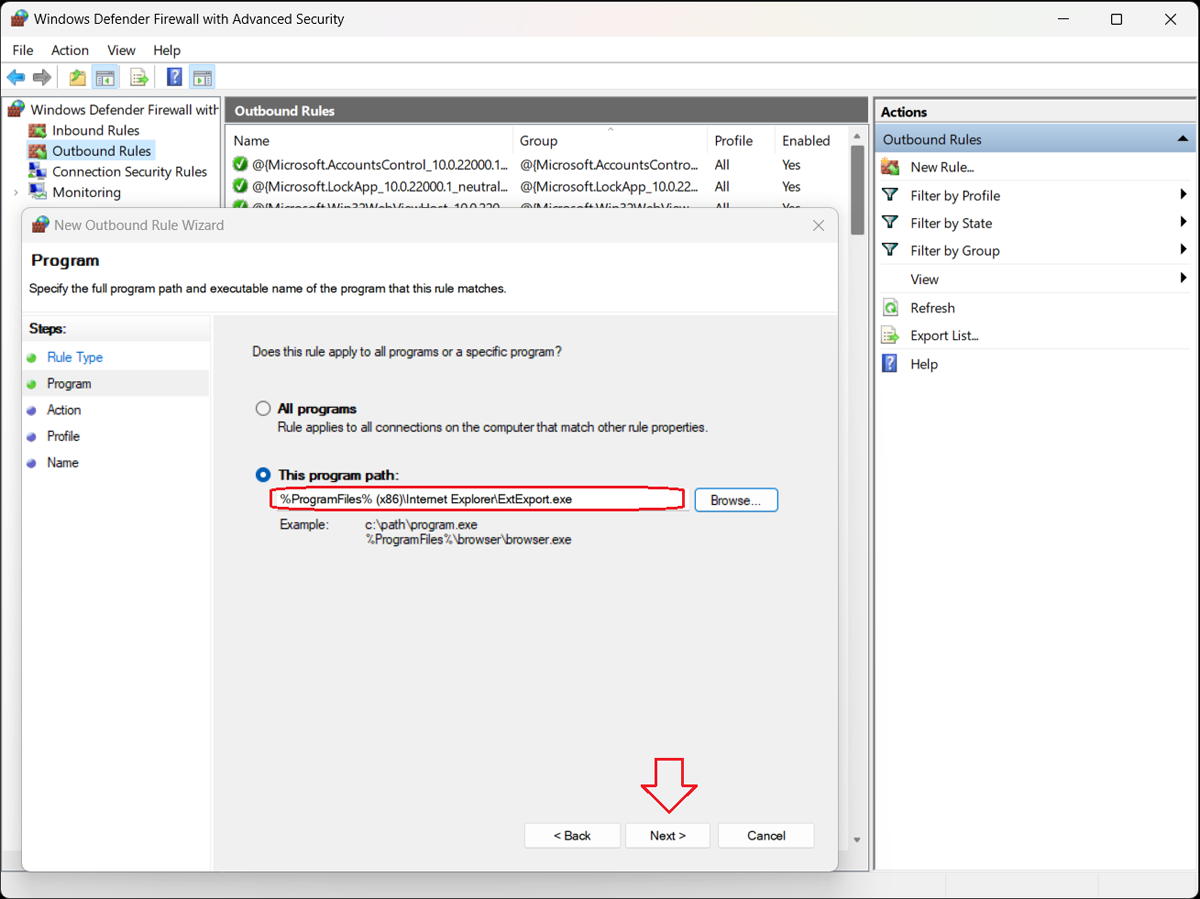
To block a specific program, select the “This program path” option and click the “Browse…” button to open the program folder.
Locate and select the executable file (.exe) for the program you want to block.
Click the “Next>” button.
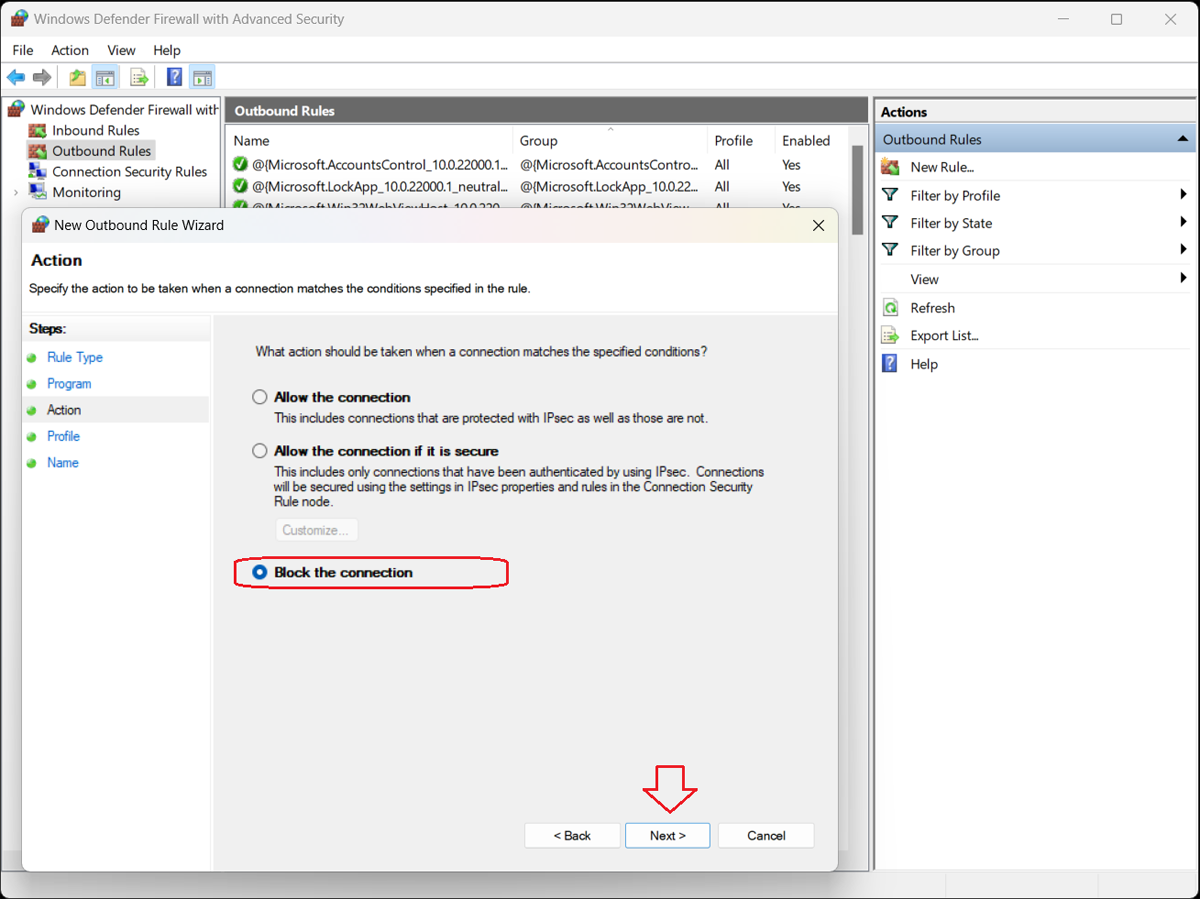
The Action window of the New Outbound Rule Wizard opens, presenting three options:
Select “Block the connection” and click the “Next>” button.
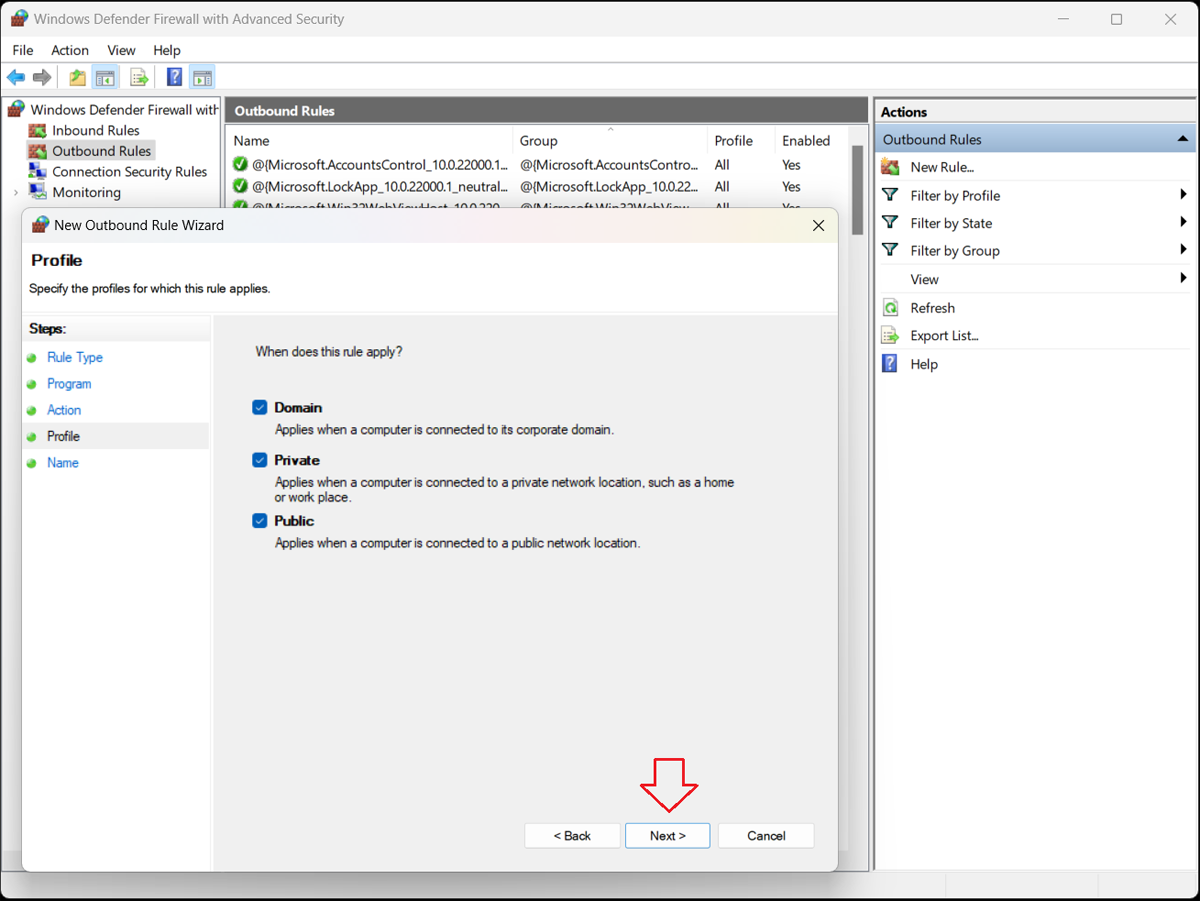
The Profile window of the New Outbound Rule Wizard opens, presenting three options:
Specify when the rule will apply and click the “Next>” button.
The Name window of the New Outbound Rule Wizard opens. In the empty fields, assign a name and description for the rule. Click the “Finish” button.
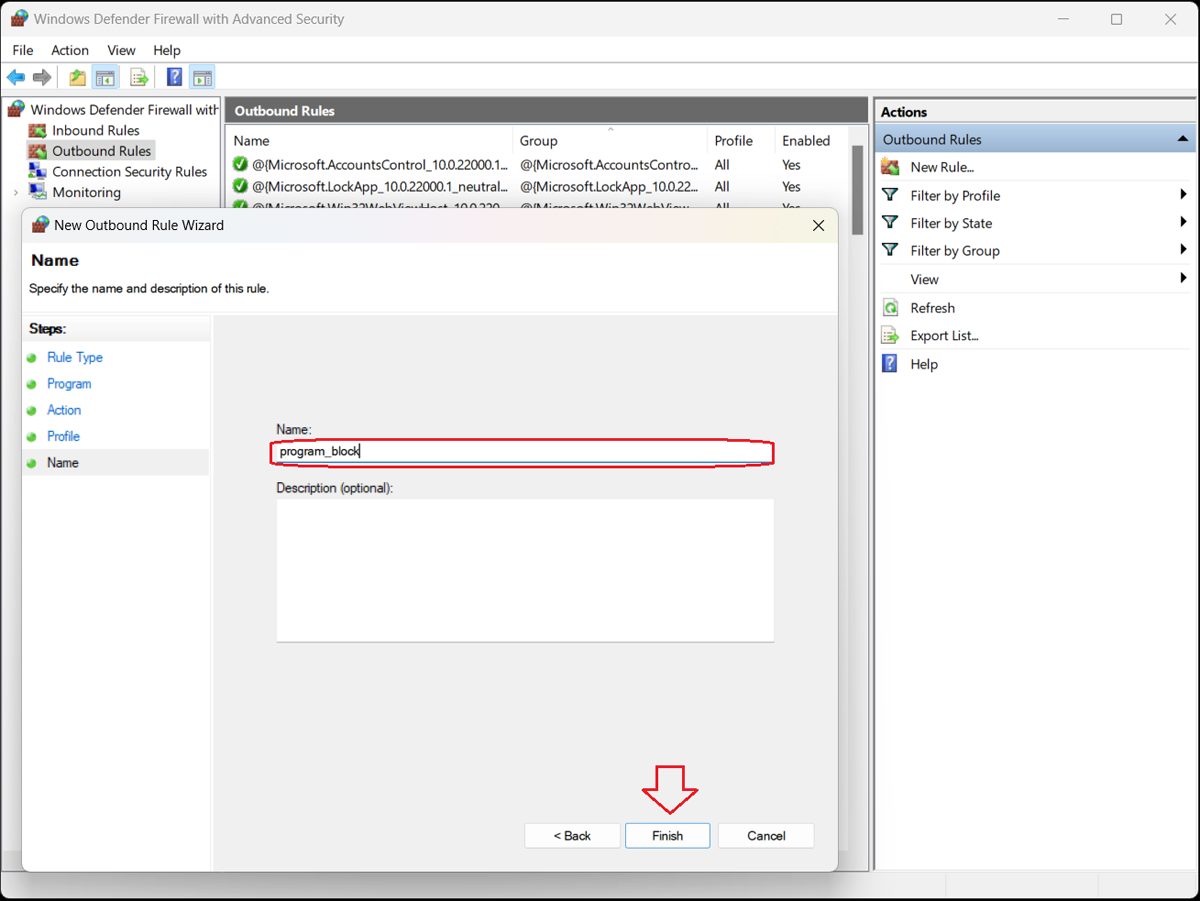
The Windows Defender Firewall with Advanced Security box lists all the existing outbound rules. Confirm that your new rule is included in the list. The program is now blocked; to unblock it, simply select and delete the rule.
You can unblock other programs the same way—to find them, sort the list by name, profile, state (enabled/disabled), or group and click Disable Rule in the right sidebar. You can also perform cut, copy, and delete rules or view their properties.
Firewalls are essential for controlling traffic in networks and ensuring protection against hackers, malware, and ransomware attacks. Most computer operating systems (OS) include built-in firewalls, and many cybersecurity vendors offer third-party firewalls with context-aware network security features that integrate with other services.
The process involved in blocking a program in a firewall can vary based on the firewall and operating system, but the steps are similar to those modeled here.
While the steps covered here apply to blocking a program in a firewall for an individual computer, enterprise-scale firewalls can be deployed to protect entire networks of computers. These enterprise-class products perform the same functions as an individual firewall by using rules to determine whether to allow access to programs and apps.
Firewalls are a critical part of network security, blocking inbound access for harmful programs and applications and preventing outbound access for installed applications and services. When configured properly and used appropriately, a firewall can safeguard your data against today’s threats.
Learn more about where to place firewalls in your network.

Al Mahmud Al Mamun is a writer for TechnologyAdvice. He earned his B.S. in computer science and engineering from Prime University, Bangladesh. He attained more than 25 diploma courses and 100 certificate courses. His expertise and research interests include artificial intelligence (AI), artificial neural networks, and convolutional neural networks.

Enterprise Storage Forum offers practical information on data storage and protection from several different perspectives: hardware, software, on-premises services and cloud services. It also includes storage security and deep looks into various storage technologies, including object storage and modern parallel file systems. ESF is an ideal website for enterprise storage admins, CTOs and storage architects to reference in order to stay informed about the latest products, services and trends in the storage industry.
Property of TechnologyAdvice. © 2026 TechnologyAdvice. All Rights Reserved
Advertiser Disclosure: Some of the products that appear on this site are from companies from which TechnologyAdvice receives compensation. This compensation may impact how and where products appear on this site including, for example, the order in which they appear. TechnologyAdvice does not include all companies or all types of products available in the marketplace.