Protect Healthcare Information with HIPAA Compliant Cloud Storage. Review this Checklist and compare Top HIPAA Storage Providers now.

Imagine, for a moment, a worst case scenario involving HIPPA compliant cloud storage.
Imagine you’re a hospital IT director who discovers a skull-and-bones graphic on his computer screen, and a patient data ransom demand for $50,000 in bitcoins. Worse, the director realizes that he was just about to implement measures to comply with the HIPAA Security Rule – but hadn’t gotten around to it yet. Maybe he could buy a winning lottery ticket and make a run for the Caribbean?
Moral of the story: administrators always need to embrace HIPAA compliant cloud storage – without delay. So let’s take a look at what this involves.
Jump to:
HIPAA Requirements for Cloud Storage
Best HIPAA-Compliant Cloud Services
HIPAA stands for Health Insurance Portability and Accountability Act, which Congress passed in 1996 to secure protected health information (PHI). The regulations cover how the healthcare industry collects, stores, shares, and transmits PHI, particularly electronic PHI (ePHI).
In 2009, Congress enacted the Health Information Technology for Economic and Clinical Health (HITECH) Act. HITECH strengthens security and privacy regulations for HIPAA-regulated data.
In 2013, the U.S. Department of Health and Human Services (HHS) Office for Civil Rights added a final rule to HITECH called HIPAA Omnibus Rule. The new set of regulations strengthens privacy rights and protections.
Covered entities (CE) are the businesses and individuals that are subject to HIPAA privacy rules: they create, receive, or transmit PHI. Covered entities include healthcare plans, healthcare providers, insurance brokerages, and more. CEs are ultimately responsible for complying with relevant regulations.
For example, HITECH governs data stored in electronic health record systems (EHR), while HIPAA governs backup data with Data Backup and Disaster Recovery Specifications.
Covered entities may contract with business associates (BA) who access ePHI on behalf of their customers. Cloud providers and managed service providers (MSP) are common business associates. Although the CE maintains ultimate responsibility for protecting and securing PHI, HITECH strengthened compliance rules for business associates.
The HITECH Act added extra protections to HIPAA, and increased noncompliance penalties. HIPAA penalties used to be just $100 per violation, and no more than $25,000 per year for the same violation. It was often cheaper for covered entities to be in non-compliance than upgrading data security and administrative systems.
The new penalties have much bigger teeth. Violation fees still start a $100, but can zoom up to $50,000 per violation depending on how shocked the regulators are at levels of non-compliance. Instead of $25,000 maximum per year for identical violations, the cap is now $1.5 million.
The healthcare industry is rapidly digitizing data, and using electronic transmission to share PHI with any number of providers. Cloud storage lets healthcare providers offload massive amounts of data to the cloud, taking advantage of the cloud’s scalability, flexibility, electronic sharing, backup, security, and reasonable cost.
But this popularity has a shadow side: can the CE ensure that their cloud provider is in HIPAA compliance? Does their HIPAA compliant offsite backup follow all regulations?
Many cloud storage providers announce that they support HIPAA, which means that their data centers and data management practices comply with privacy and security rules. However, they may or may not help their CE customers with configuration. This puts CEs at risk of non-compliance because they did not understand how to configure their own cloud data settings to be compliant. And some cloud providers may claim HIPAA compliance, but are unwilling to sign business associate agreements (BAA).
A signed BAA confirms that the cloud provider is HIPAA-compliant with physical and digital security, ePHI privacy, storage management and backup technology, user authentication, and administrative practices.
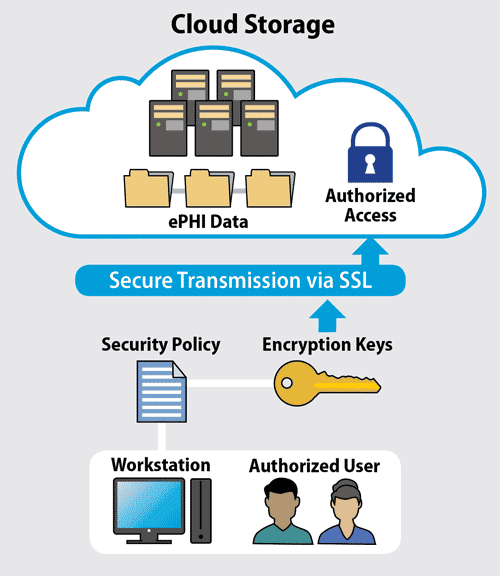
HIPAA compliant cloud storage requires a well-defined security policy, compliant file transfer, and secure infrastructure.
When reviewing a cloud provider, review how well they are compliant with HIPPA’s three major ePHI protection rules: the HIPAA Privacy Rule, the HIPAA Security Rule, and the HIPAA Breach Notification Rule:
HIPAA compliance in the cloud doesn’t happen by accident. First, when you’re looking for cloud provider, make sure that they publicly state HIPAA compliance. Not all HIPAA-compliant cloud providers will sign BAAs, so it’s time to read the small print.
Know the services that you want to contract with a provider. If any of the services involve ePHI, then ask the provider if they’re willing to sign a BAA for those services. Also ask questions around risk assessment, infrastructure, encryption, physical security, and protections in multitenant environments.
Look for cloud providers that are HIPAA-compliant and that will sign a BAA. That does not mean the CE can sign on the dotted line and walk away. Most HIPAA-compliant cloud providers operate under a shared responsibility model, where the CE and BA share compliance responsibilities. Here are some examples:
Google’s HIPAA BAA covers Google Cloud Platform (GCP) infrastructure. The CE is still responsible for creating a secure environment and applications they build in GCP, including backing up ePHI. Google will also sign a BAA for select G Suite applications including Gmail, Calendar, Docs, Sheets, Slides, and Forms.
Microsoft offers a BAA for most Microsoft Online applications, including Office 365. Microsoft also signs BAAs for enterprise cloud services running on Azure.
Box is HIPAA compliant and will sign a BAA for its healthcare customers. Box also enables secure DICOM file (digital healthcare records) viewing and sharing.
Amazon signs a BAA for Amazon S3 Glacier data storage. It also offers a signed BAA for Amazon Web services, but customers must configure their own HIPAA compliant cloud storage. AWS will advise on the best configurations. Liked Google Cloud Platform, AWS subscribes to the shared responsibility model.

Christine Taylor is a writer and content strategist. She brings technology concepts to vivid life in white papers, ebooks, case studies, blogs, and articles, and is particularly passionate about the explosive potential of B2B storytelling. She also consults with small marketing teams on how to do excellent content strategy and creation with limited resources.

Enterprise Storage Forum offers practical information on data storage and protection from several different perspectives: hardware, software, on-premises services and cloud services. It also includes storage security and deep looks into various storage technologies, including object storage and modern parallel file systems. ESF is an ideal website for enterprise storage admins, CTOs and storage architects to reference in order to stay informed about the latest products, services and trends in the storage industry.
Property of TechnologyAdvice. © 2026 TechnologyAdvice. All Rights Reserved
Advertiser Disclosure: Some of the products that appear on this site are from companies from which TechnologyAdvice receives compensation. This compensation may impact how and where products appear on this site including, for example, the order in which they appear. TechnologyAdvice does not include all companies or all types of products available in the marketplace.