iSCSI is a storage protocol for connecting computers and storage devices over an IP network. Learn more about how it works and its benefits.

Internet small computer systems interface, or iSCSI, is a storage area networking transport protocol that allows client devices to access block-level storage devices over an Ethernet network. Like Fibre Channel, iSCSI can be used for storage area networks (SANs) and works on shared networks or dedicated storage networks. It cannot, however, support file access solutions like network attached storage (NAS) or object storage solutions, which use different transport protocols. This article explains how the iSCSI protocol works and the benefits and limitations of using it.
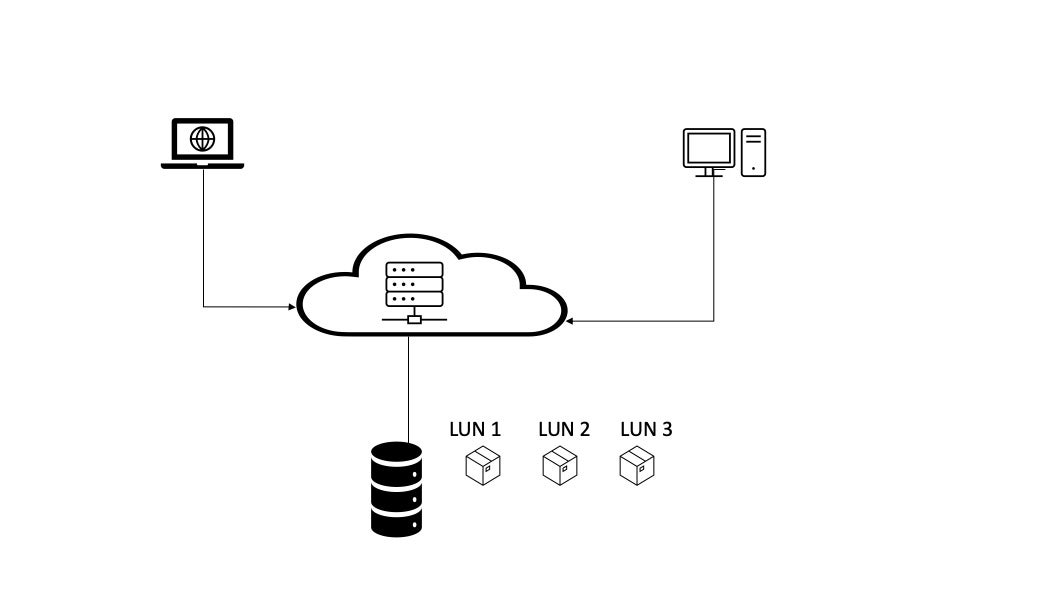
In a storage area network, or SAN—an independent high-speed network of connected switches, hosts, and storage devices—the iSCSI protocol is used to transmit data over the Ethernet network that connects users to the storage devices. iSCSI functions in the transport layer. It makes it possible for network connected devices to appear local to users.
A data packet, or unit of data bundled together for network transit, is made up of the data payload and a header that stores information about the packet, including destination and origin IP addresses. It’s also called a datagram. A data unit in the TCP transport layer is called a segment, and a data unit in the link layer is called a frame.
When an end user application initiates a request to the operating system, an appropriate SCSI command and data request are generated. A packet header is added to the request and encapsulated as a protocol data unit (PDU) containing SCSI data inside the TCP header as part of an Ethernet frame. The entire frame is then transmitted over the Ethernet network.
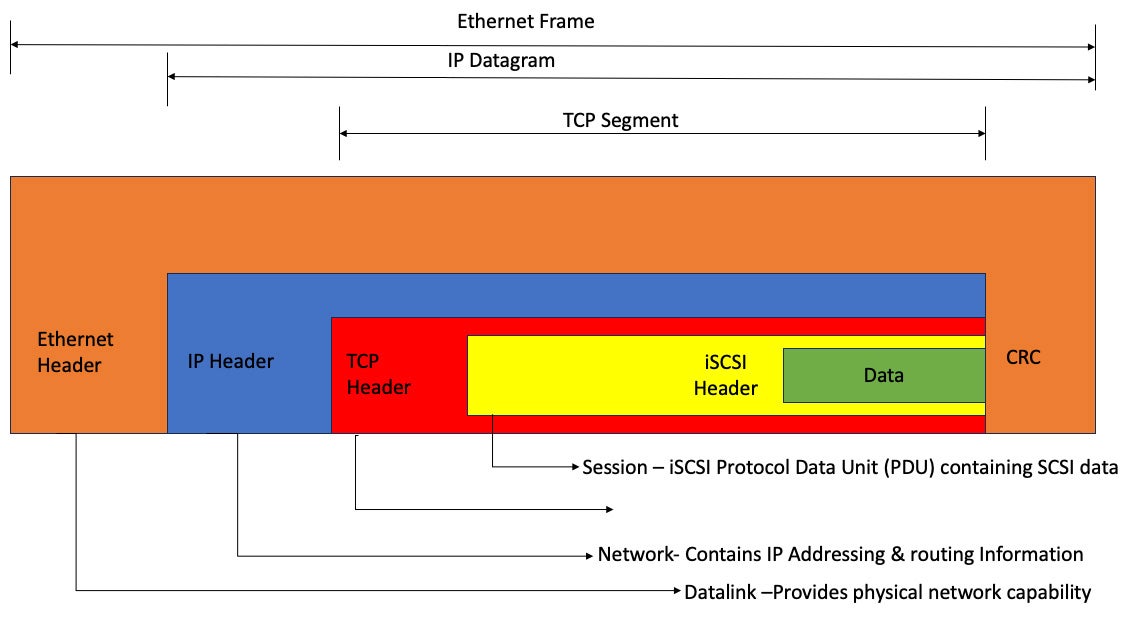
When the Ethernet frame reaches its final destination, the target datalink layer removes the frame encapsulation and sends the results to the network. The iSCSI protocol disassembles the packets and separates the SCSI commands, allowing the operating system to see the storage device as a locally connected SCSI device.
The SCSI commands are sent to a SCSI controller, and the controller diverts those SCSI commands to the SCSI storage device. The iSCSI protocol is bi-directional and can also return data in response to the original request.
The iSCSI protocol uses iSCSI initiators and iSCSI targets. The PDU depicted in Figure 1 communicates between the initiator and the target. The information in the PDU helps establish a session, transport iSCSI commands, move data, and provide node detection information.
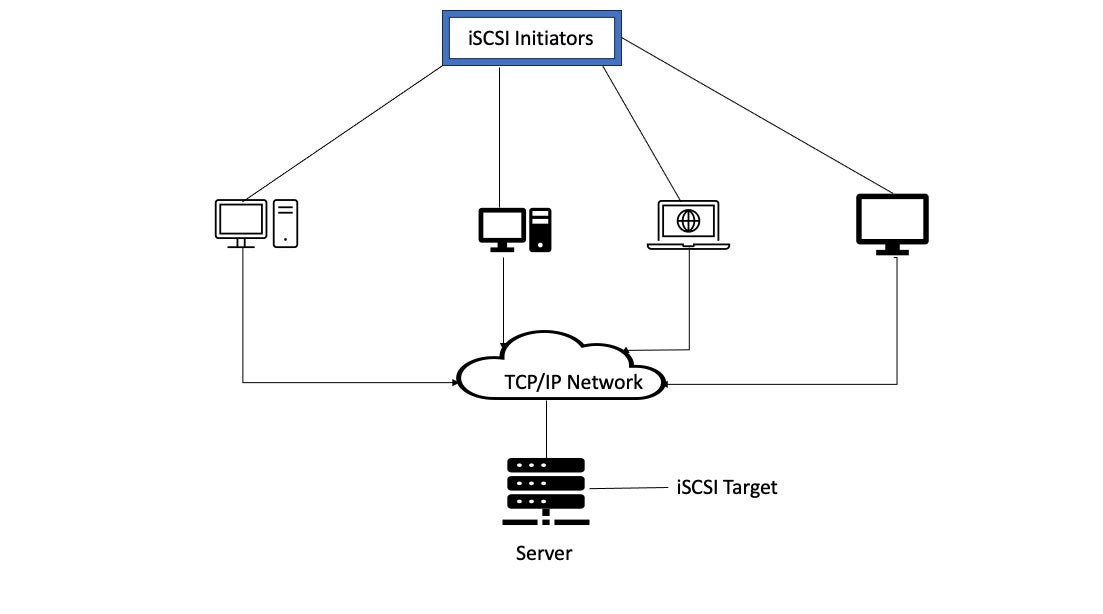
The initiator resides on the client machine. It can be initiated by either software or hardware, but software initiation is much more common. Servers are the iSCSI target and can receive initiator requests on one or more TCP/IP connections.
Because the iSCSI network and protocol can transmit data over local area networks, wide area networks, and the Internet, the performance of an iSCSI network varies greatly depending upon variable factors, including the speed of the network and storage controller and the controller configuration.
Ethernet switches and media can operate at speeds of 1 GB, 10 GB, 40 GB, and 100 GB. iSCSI network speed is usually configured for 10 GBs infrastructure networks.
iSCSI and Fibre Channel (FC) are both effective and popular for transferring a large amount of data. The following chart shows the major differences between iSCSI and FC.
| iSCSI | Fiber Channel | |
|---|---|---|
| Infrastructure | The same infrastructure is deployed in the user and server network | Dedicated infrastructure separated user and server network |
| CPU Load | Higher than Fiber Channel | Lower than iSCSI |
| Supported Distance | Distance is not limited | Limited distance |
| Deployment | Easy to manage and simple | Labor-intensive and complex |
| Latency | Higher than Fiber Channel | Lower than iSCSI |
| Cost | Less Expensive | More Expensive |
| Applicability | Well-suitable for low input/output application | Well-suitable for high input/output application |
Fibre Channel SAN is great for businesses with enough budget and expertise to implement and manage a dedicated fiber channel network. iSCSI SANs run on Ethernet networks and do not always need dedicated network hardware. iSCSI SANs are good for businesses that require high-performance workloads without deploying dedicated network hardware.
iSCSI offers a wide range of benefits for enterprises that deploy it as part of a SAN. Here are the most common:
Though iSCSI offers many benefits, like most technologies, it also has limitations. Here are the msot common:
The need for high speed data transfer and high capacity data storage have become essential to enterprise data functions. Storage area networks are a viable solution to both of these needs. SANs using the iSCSI protocol run on Ethernet networks, making them a good choice for businesses with existing networks that also require high-performance workloads but don’t want to purchase and install dedicated network hardware.
Read about the five types of enterprise data storage to learn more about the various ways businesses choose to store their data and make it accessible to users.

Don Hall is a contributing writer to Enterprise Storage Forum, where he covers data storage technology, storage hardware and software, and data networking. He worked for more than two decades as an IT Supervisor for the federal government and as IT Operations Supervisor for an IT Military Command managing programmers, cybersecurity staff, and infrastructure and networking personnel. Previously he worked as an application programmer. Don earned a B.S. in Business Information Systems from San Diego State University and has certificates in Technical Communication and web development with an emphasis in Java/Open Source. He has also had an active CompTIA Security + (ce) since 2011, and a Network +(ce) since 2015.

Enterprise Storage Forum offers practical information on data storage and protection from several different perspectives: hardware, software, on-premises services and cloud services. It also includes storage security and deep looks into various storage technologies, including object storage and modern parallel file systems. ESF is an ideal website for enterprise storage admins, CTOs and storage architects to reference in order to stay informed about the latest products, services and trends in the storage industry.
Property of TechnologyAdvice. © 2026 TechnologyAdvice. All Rights Reserved
Advertiser Disclosure: Some of the products that appear on this site are from companies from which TechnologyAdvice receives compensation. This compensation may impact how and where products appear on this site including, for example, the order in which they appear. TechnologyAdvice does not include all companies or all types of products available in the marketplace.