Container security tools are a type of software that automates vulnerability searches and notifies developers and IT teams of possible threats in container environments. Containers—packaged applications and all related code that allows an application to run in an isolated environment—are not inherently secure. Though they have some built-in security features, they require additional tools to […]

Container security tools are a type of software that automates vulnerability searches and notifies developers and IT teams of possible threats in container environments. Containers—packaged applications and all related code that allows an application to run in an isolated environment—are not inherently secure. Though they have some built-in security features, they require additional tools to ensure protection in development and runtime environments.
This guide covers the best container security tools, as well as features your business should look for and questions to ask before purchasing a product.
Best Container Security Solutions
Best solution for DevOps teams that want heavy security in development
Geared toward the software supply chain, Anchore Enterprise is a security and compliance solution for businesses that need to improve their development environment’s security. Anchore can run on any container environment, either on premises or in a public cloud. It focuses on analysis and policy-based compliance for containers—put simply, container images are inspected and either pass or fail.
Anchore is developer-centric, providing assistance to DevOps teams as they work to secure applications in their early stages. Anchore also offers two open-source container security tools: Syft, for generating software bills of materials (SBOMs) and viewing dependencies with the command line interface (CLI) tool, and Grype, for scanning container images and generating a list of vulnerabilities. Users can also join the Anchore community Slack channel.
Anchore has four enterprise plans: Team, Business, Ultimate, and Ultimate+. Pricing for all plans is available on request from Anchore.
Also read: 7 Essential Compliance Regulations for Data Storage Systems
Best for sandboxing
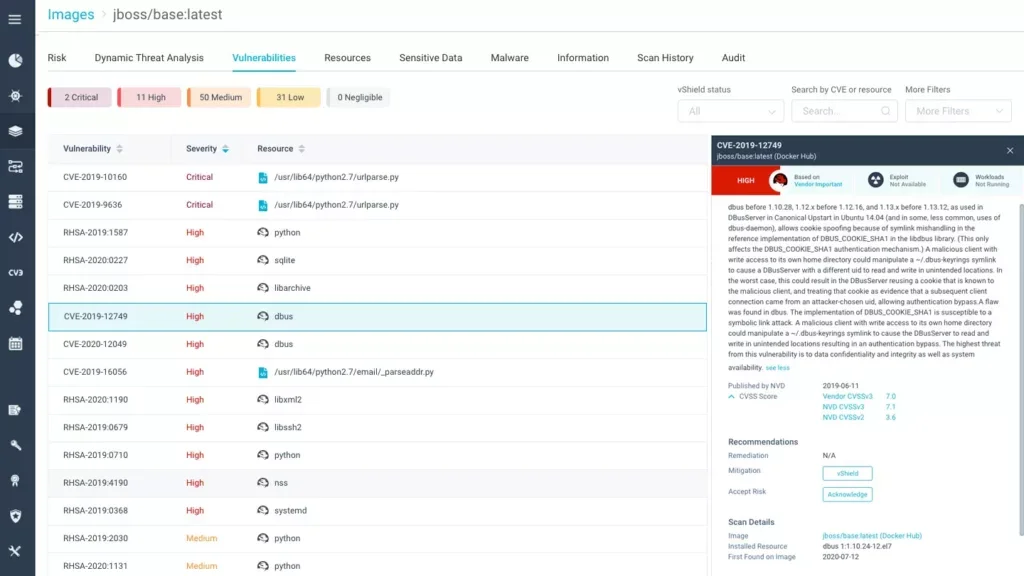
Aqua Security, also known as Aqua or AquaSec, is a cloud-native solution that offers container security, Kubernetes security and serverless security products, among others. Aqua supports Linux and Windows containers and provides both on-premises and cloud deployment options. Using Aqua, businesses can view scans of container images and a rank of their vulnerability severity. They can also access audit data for Kubernetes runtime environments, which improves compliance.
Aqua Dynamic Threat Analysis (DTA) is a product that analyzes images for behavioral anomalies and locates advanced malware, placing images in a secure sandbox. It can also prevent images from being deployed in a production environment. DTA provides activity data on such threats as code injection backdoors and cryptocurrency miners. Aqua Security is a good choice for teams that want to perform advanced threat analysis and sandboxing on their containers.
Potential customers for the entire Aqua platform can request a demo. Pricing for the cloud security tool is based on workload numbers; pricing for dev security is based on total number of code repositories. Contact Aqua Security for more detailed pricing information.
Best for large enterprises and security teams
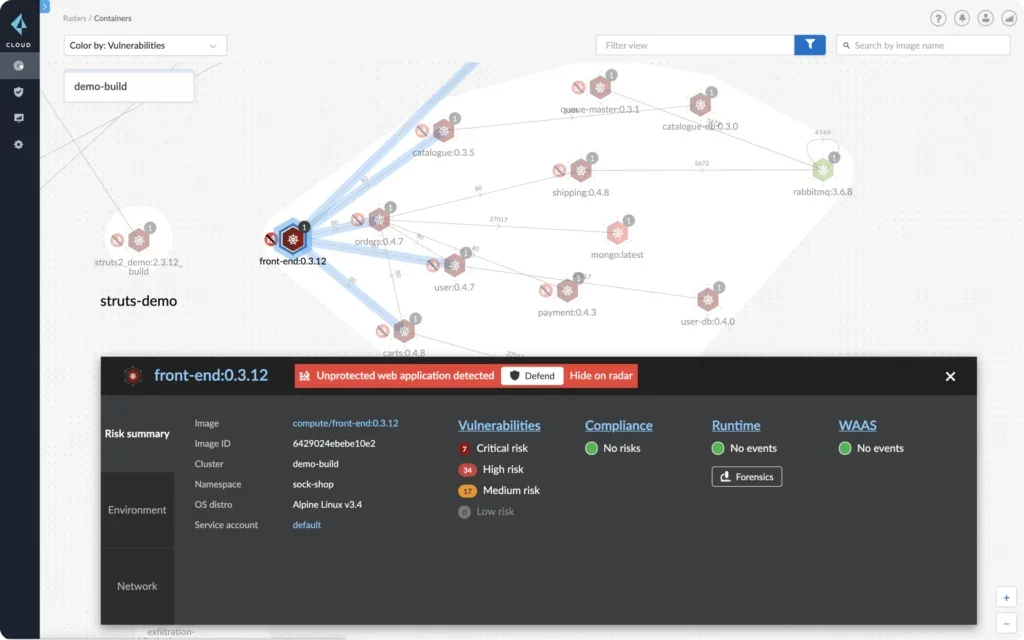
Palo Alto Prisma Cloud, formerly Twistlock, is an integrated security solution for containers and workloads that allows businesses to manage threats to their public cloud workloads. Prisma Cloud supports both AWS and Azure. The platform consists of seven core solutions that integrate with each other. These include Cloud Security Posture Management, Code Security, Cloud Workload Protection and Cloud Network Security. Container security is one module of the Cloud Workload Protection solution.
Prisma Cloud is good for mid-sized and large enterprises that need high network visibility and security. It provides DevOps and security operations teams with visibility for cloud and container environments. Implementing and using the solution successfully requires sufficient planning and ownership for DevOps and security teams.
Prisma Cloud enterprise pricing is done through credits, which customers can purchase in increments of 100. Tools and specific features are measured by number of credits per resource instance. Credits can be purchased through Palo Alto directly, through channel partners or through marketplaces. Contact Palo Alto for more detailed information on credit pricing.
Best for large enterprises that want a broader cloud platform with a container module
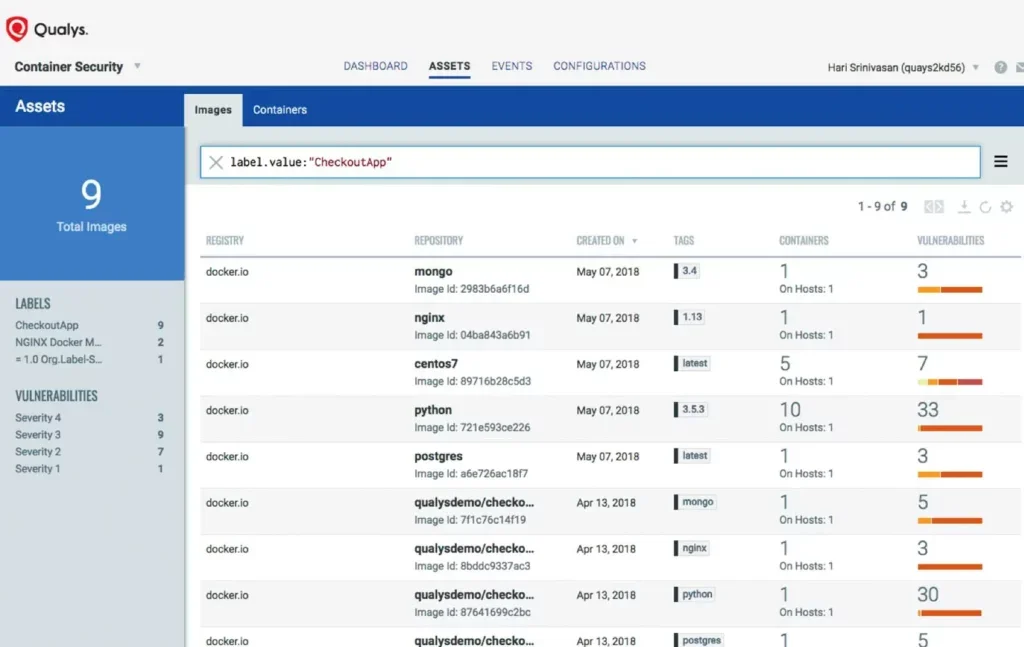
Qualys Container Security is one of 24 applications that fall under the Qualys Cloud Platform umbrella. The Cloud Platform is available for the cloud and on-premises container deployments. Qualys’ Container Runtime Security (CRS) feature is an add-on that allows enterprises to monitor container runtime. Administrators set policies that govern container behavior, and CRS reveals when those policies have been broken during runtime.
Qualys’ native container sensor rests on Docker hosts and monitors container deployments. Users can view metadata for each image and each container, including container host information and the container’s privilege status. They can also view association to other containers on the same parent image.
Qualys offers a free trial. Pricing for the platform is based on the Cloud Platform Apps in the user’s environment, as well as the number of IPs, web applications and user licenses. All Cloud Platform subscriptions include training and support.
Best for all-Kubernetes environments and enterprises running other OpenShift products
Red Hat recently acquired container security solution StackRox to create Red Hat Advanced Cluster Security for Kubernetes, which meets security and compliance needs for Kubernetes and Google Kubernetes Engine environments. Red Hat also offers a StackRox community for open sourcing and managing Kubernetes cluster security code. The underlying code for the Red Hat solution is open source.
StackRox users have compliance capabilities to identify whether nodes and clusters conform to regulations like National Institute of Standards and Technology (NIST) and HIPAA and show data to auditors. It also allows businesses to remediate misconfigurations, including excessive privileges, and to create custom policies for configuring builds and deployments.
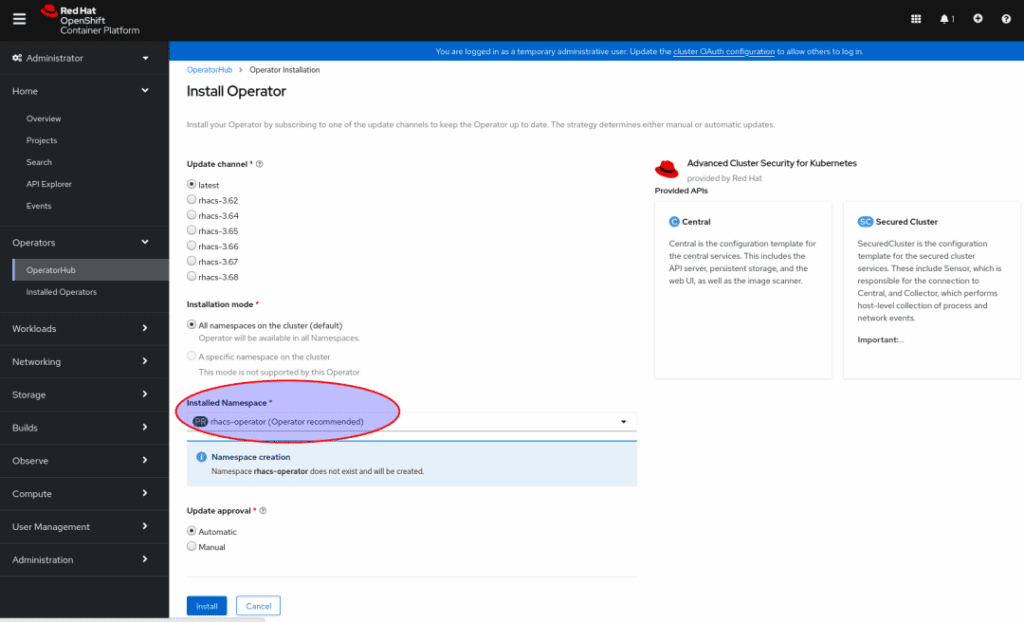
Red Hat offers two pricing plans for its Advanced Cluster Security for Kubernetes. The Standard plan, which has standard support, costs $500 per instance, billed annually. The Premium plan costs $750 per instance, billed annually.
Best for developers working in code repositories
Snyk offers a security solution specifically designed with developers in mind. It searches for license violations in Docker images and provides a vulnerability report for each package in a repository. Snyk supports a variety of programming languages, which makes it easier for customers to implement. It permits many integrations for developers, including GitHub and GitLab connections.
Snyk Advisor offers safety and history of third-party dependencies, allowing users to search and compare many open-source projects. It ranks them on a scale from 0 to 100, giving them a Package Health Score.
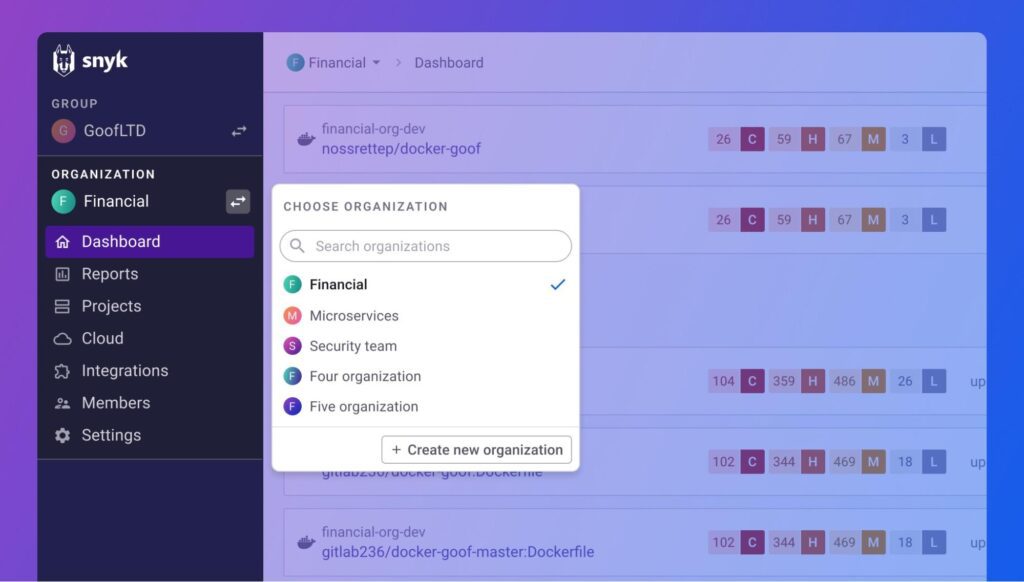
Snyk offers three plans: Free, Team and Enterprise. The Free plan is suitable for startups and very small businesses. The Team plan costs $52 per month for each contributing developer. The Enterprise plan has custom pricing, and potential customers can request a live demo from Snyk.
Best solution for customer and technical support
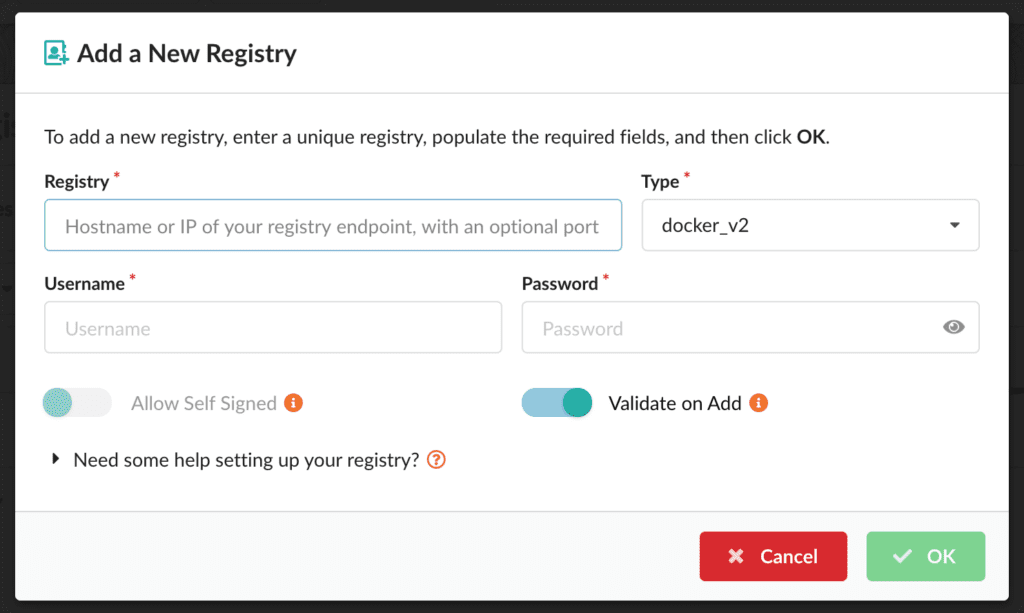
 Sysdig Secure is a product for container, Kubernetes and cloud security that operates in both cloud and on-premises environments. Sysdig users can automate scans of CI/CD pipelines and registries and block vulnerabilities before a container goes into production. The vulnerability management solution also scans both containers and hosts so that users need only one tool to scan both. Sysdig works with Prometheus, an open-source application and Kubernetes monitoring tool.
Sysdig Secure is a product for container, Kubernetes and cloud security that operates in both cloud and on-premises environments. Sysdig users can automate scans of CI/CD pipelines and registries and block vulnerabilities before a container goes into production. The vulnerability management solution also scans both containers and hosts so that users need only one tool to scan both. Sysdig works with Prometheus, an open-source application and Kubernetes monitoring tool.
Sysdig offers continuous cloud security posture management (CSPM), which includes misconfiguration notifications and compliance validation for a number of regulations. It also provides zero trust network security and Kubernetes-native microsegmentation.
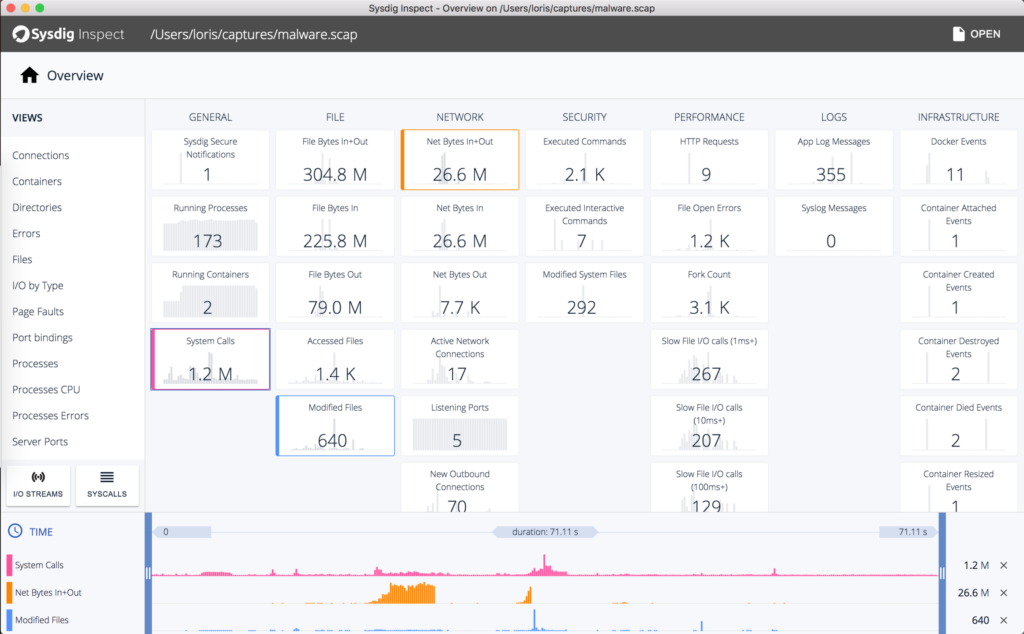
Sysdig Secure offers a free trial. Specific pricing is available from the vendor, but current marketplace pricing is around $720 per host, billed annually.
Often, container security is one product or component of a larger security tool; many providers offer cloud security services under which container security falls. Features of container security include:
Some tools focus more heavily on development, providing security features for developers to use while designing and testing source code. Other tools provide heavy runtime security and threat remediation.
If your business plans to buy container security software, consider the following points during the evaluation process.
A security tool needs proper context to avoid throwing the aforementioned false positives. For example, does the tool know if a particular application is actually accessing sensitive company data at the time? Some container security solutions have the capability to identify if a vulnerability within the container is being actively exploited and prioritize it based on that.
Select a container security solution that fits your enterprise’s price range. Some security solutions will have a lower price, while others are suitable for large enterprises with a high budget. Similarly, your business will want to choose a solution that’s a good fit for your security and dev teams. More experienced teams may enjoy thoroughly customizing a more complex solution, while small or junior teams will likely need something with an easy-to-understand interface.
Some solutions focus more on security in development, while others offer real-time threat remediation. Aside from knowing what your business needs, note that having solid threat response capabilities will give you a greater advantage if an attack such as ransomware breaches your container orchestration platform. On the other hand, a dev-focused solution will benefit a large application development team.
Highly responsive threat detection solutions create alerts. Look for a container security tool that limits false positives and that provides a number of alerts that your IT and security teams can manage. Too many alerts overwhelm admins, waste time and increase the likelihood of a breach.
New, fast-growing technologies need to be closely monitored and quickly secured, and containers are no exception. Security for containers is interesting because it requires protection both during the development process and during runtime. Both should be prioritized. Businesses with growing container environments should invest in a solution specific to containers and orchestration engines so they can detect threats and halt them.
Read more about the market for container management technology.

Jenna Phipps is a staff writer for Enterprise Storage Forum and eSecurity Planet, where she covers data storage, cybersecurity and the top software and hardware solutions in the storage industry. She’s also written about containerization and data management. Previously, she wrote for Webopedia. Jenna has a bachelor's degree in writing and lives in middle Tennessee.

Enterprise Storage Forum offers practical information on data storage and protection from several different perspectives: hardware, software, on-premises services and cloud services. It also includes storage security and deep looks into various storage technologies, including object storage and modern parallel file systems. ESF is an ideal website for enterprise storage admins, CTOs and storage architects to reference in order to stay informed about the latest products, services and trends in the storage industry.
Property of TechnologyAdvice. © 2026 TechnologyAdvice. All Rights Reserved
Advertiser Disclosure: Some of the products that appear on this site are from companies from which TechnologyAdvice receives compensation. This compensation may impact how and where products appear on this site including, for example, the order in which they appear. TechnologyAdvice does not include all companies or all types of products available in the marketplace.